When firms think about cybersecurity, they’re tempted to focus on the tech. Hopefully, you’re already having internal conversations about which tools you need to fight phishing or to keep your mobile devices safe.
One area where we’ve seen a lot of firms struggle, though, is in figuring out what to do when something BAD happens. The SEC Cybersecurity Guidance actually has quite a lot of detail when it comes to incident response.
Reading the guidance will help, but firms struggle to make incident response real.
The whole point of having an incident response plan is so you will know exactly who will do what when something bad happens. In this article, we’ll help you to figure out whether your Incident Response plan is good enough to keep you safe and comply with the SEC Cybersecurity Guidance.
What is Incident Response?
Incident response is actually very simple: “What’s your plan when something bad happens?”
Your business’ response to a cybersecurity incident should be just as clear and repeatable as the process you use to send quarterly investment statements or to approve a wire transfer before it goes out the door. Auditors want to see a process, not just a document.
What is an Incident?
First, what is an incident? Broadly, it’s anything bad that happens in your firm.
Some specific examples include:
- An employee violates your policy
- A hacker accesses your systems without approval
- Someone steals your data
- Your Internet is unavailable for an extended period of time
- A computer is damaged, lost or stolen
- A virus or ransomware is installed on your computer
- You get a phishing message and someone clicks on it
- A smartphone is lost or stolen
- A natural disaster affects your ability to work (but you already have this covered in your business continuity plan, right?)
This is far from an exhaustive list.
The first step you should take in building an Incident Response plan is to talk as a team about the kinds of incidents that are likely to affect your firm. Make a list, and discuss how you’ll handle each type of incident.
Incident Response Policy
Many firms have their compliance attorneys write an incident response policy as part of their overall cybersecurity/compliance policy. SEC Cybersecurity Guidance demands that you have a policy, essentially, so it is a necessary and great first step. There are many good policy templates to be found online, like this one.
Firms sometimes ask if it needs to be a standalone policy document, or if it can be a section in their existing Cybersecurity Policy or Compliance Manual. Either way is fine.
Once the policy is done, many firms make the mistake of stopping there. They treat is as just a compliance exercise. They don’t have a conversation about what will really happen when the hits the fan. This is a concerning approach, for many reasons.
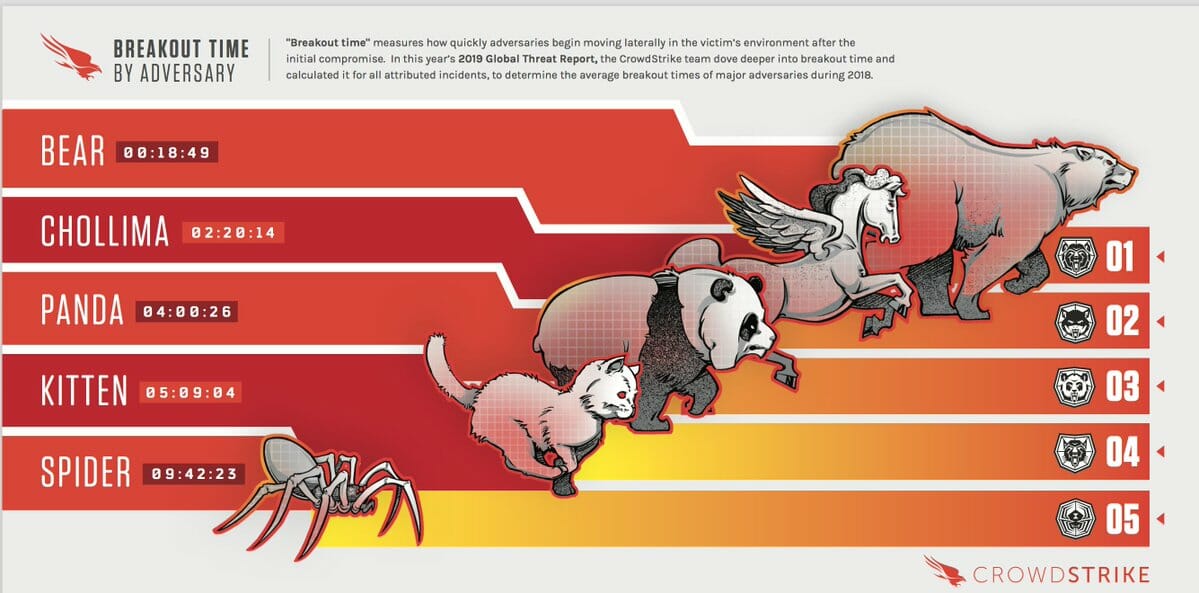 Based on a recent Crowdstrike report, it only takes a seasoned attacker 18 minutes to start moving around from machine to machine in your network (called ‘lateral movement’).
Based on a recent Crowdstrike report, it only takes a seasoned attacker 18 minutes to start moving around from machine to machine in your network (called ‘lateral movement’).- The faster you respond the better you will fare. The less chance there is that your data will be stolen, and you’re more likely to stop any financial losses.
- Knowing what to do BEFORE the incident occurs, relieves a whole lot of stress on your team when it does occur.
SEC Cybersecurity Guidance: Incident Response (in real life, not jargon)
Let’s walk through a real example to show you how to bring your policy to life.
An employee calls you because she’s seen something strange in their email.
She was looking in her Sent folder, and had a bunch of emails in there that she didn’t recognize.
All of the emails were sent to some weird looking address, like dk8938@yahoo.com. She didn’t own or recognize that email address.
Oh, crud. Someone is in your email system who does not belong.
This is definitely “Unauthorized Access.”
Here’s what a real incident response might look like. Of course, your process (and how it’s written in your policy) might differ, but use this real example to make sure your policy is at the right level of detail.
Escalate the Incident
A lot of companies struggle with this.
You need to teach your staff to escalate an incident as quickly as possible.
Remember — 18 minutes. The clock is ticking.
You need to explicitly train your staff on how to recognize an cybersecurity risk or incident. Make sure that people know that they’re not going to get in trouble for escalating an incident. And make sure that they have the appropriate sense of urgency when they see something weird or wrong.
In your training, teach them to trust their gut. It’s better to escalate and have it turn out to be nothing than to sit on it for a day while a hacker steals your customer database.
Make sure your process is crystal clear on how to escalate. Give them a name, an email address, and even a phone number to use. Some companies even go so far to create anonymous mechanisms, like an anonymous online form. A tip box in the lunch room can work, but only if someone checks it regularly.
Convene the Incident Response Team
You’ve seen the weird email, the situation is ESCALATING, and you need to get the right people together. Pull together your IT, Cybersecurity, Compliance, and Legal teams.
Your policy should name and specifically identify the “incident response team”.
GET THEM TOGETHER, face-to-face or on a web conference and look at the situation together. Resist the temptation to just talk about this in a slow-motion email chain or by everyone making one-on-one calls to everyone else. Get everyone together, URGENTLY, and stay on the phone while you figure out what’s going on.
Also, resist the temptation to just delegate the investigation to your IT team. Being together, in real time, means that you’ll be able to respond much more quickly based on what you find.

Remember — 18 minutes to breakout!
When you’re meeting, keep these four questions in mind:
- Figure out what happened. Identify the earliest possible moment that the attack started, and any evidence to find when it could have ended. Pull every log you possibly can for this timeframe.
- Your first priority? Figure out whether it is STILL happening.
- Focus on what was stolen, if anything. What did the attacker take? Is there damage left behind? Affected systems? Was it to the ad for an upcoming ad for an upcoming seminar you’re doing? No big deal. Was it your customer database? BIG DEAL. ***
- If you are in IT, stay focused on figuring out what happened. Your first inclination will be to say “we could have prevented this with two-factor authentication” or “we should turn up our logging levels.” Save fixes and solutions for later. Figure out the timeline of what happened, and how.
PRO TIP: As soon as you get any indication that sensitive data was compromised, pull in your attorney. If you don’t have in-house legal counsel, get your external counsel involved immediately. Beyond getting their experience and advice, you also want them to advise you on the appropriate use of attorney-client privilege. Anything you gather or document may later become part of legal action, and privilege will help.
If you have cyberbreach insurance, your insurance company will also have attorneys on retainer that you can use.
Contain the Incident
- If the attack is still going on, you need to stop it.
- Be careful, though! You can’t just start pulling plugs out of walls or shutting down computers (even though you’ll be tempted).
- Take the time to discuss how you will stop the attack and make sure you don’t destroy any evidence.
- Make sure IT experts are involved. Even something as innocuous as shutting down a computer that is under attack can wipe crucial evidence.
- Common containment could include remote wipe of a computer, resetting passwords, removing a computer from the network (but leaving it on), etc.
Phew. Now that the incident is contained, you can move out to figure out what to do.
What Was Stolen or Accessed?
- Figure out, in detail, what was stolen or what systems were affected.
- You want specific dates, times, filenames, emails.
- Go through everything as thoroughly as you can.
- You’ll probably find out that you’re missing some key log files, or some other data that would help you to see what happened. Don’t get demoralized. Work with what you have to get as complete a picture as possible.
- You might need a forensic expert who can use advanced tools to piece together what happened. These teams can be very expensive, but many cybersecurity insurance policies will cover this cost.
Notification
- Many different laws require you to notify clients impacted by breaches. This is a difficult and sensitive operation, and should be well thought-out in advance.
- For large breaches, you may be required to notify the media.
- Laws vary by state and by industry. Know which jurisdictions you fall into.
- To understand what your notification obligations are, you need to work with your attorney. They’ll know which laws apply and how to comply.
Lessons Learned?
- It’s VERY important that you don’t skip this step! Many firms do, at their own peril.
- Now that the pressure is off, it’s time to hear all of those ideas from the IT team to make sure this incident doesn’t happen again.
- Figure out how to close the loopholes that allowed the breach the first time, this may include process changes, configuration changes, training and new systems entirely.
- Also, evaluate how you did as an “incident response” team. Even if this exact problem never comes up again, how can you be more effective next time?
At the end of the incident, someone in your compliance or cybersecurity team should put together a single document that describes what happened, how it happened, and the solutions that will be put in place to prevent it from happening again.
The SEC Cybersecurity Guidance for incident response is thorough, but you need to make it real.
Making an Incident Response policy that works for your business BEFORE an incident happens is critical to limit the damage done to your firm and your customers. Your policy means nothing without having the right team, training, and planning to figure out how you’ll handle possible breaches. As you can see, there’s a lot that goes into getting prepared to respond to an incident. Hopefully your team has the expertise and bandwidth to handle it.
If not, we can help. Our SEC Cybersecurity Service is the easiest way to build a strong cybersecurity program.

