What is phishing?
How can you protect your data at home and work?
Phishing is the #1 cause of data breaches. Even with all the technical protection in the world, phishing emails sneak in. Protect yourself and your company by learning more about phishing and how to spot phishing messages.
Phishing is a cybercrime where you are tricked into clicking a link or giving up personal information, such as credentials or credit card numbers.

Phishing emails can seem obvious when they are riddled with typos and grammatical errors. But they can also be sophisticated, convincing and incredibly hard to detect. There are various types of phishing, including whaling, spear phishing, smishing, vishing, angler phishing and more.
Phishing attacks can be devastating to organizations of all sizes. The implications include financial costs, user downtime, reputation damage, loss of intellectual property, loss of revenue and clients, lost data and more.
It’s important to understand the various phishing attacks and how to identify them.
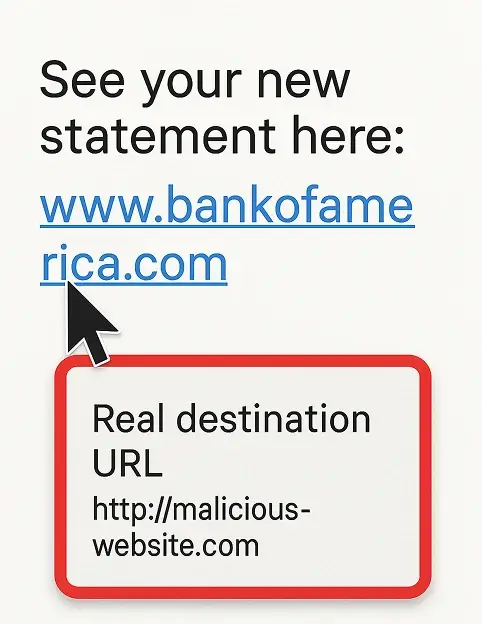
Typically, when you think of phishing, you think of email phishing. Hackers impersonate known brands or people to try to convince people to give up information or click a certain link.
Smishing is a phishing text message. Typically, they will include a link that installs malware when clicked.
Thanks to sites like LinkedIn and company websites, cybercriminals can easily find the name and email address of CEOs or senior leaders intending to impersonate that person. The impersonated leader will often ask for money transfers, gift card purchases, or ask to review a PDF.
Spear phishing is similar to whaling, as it involves cybercriminals doing some research to create targeted phishing emails. Hackers could use specific information such as age, location, interests, employers, friends, and family to trick you into thinking they are trustworthy.
Vishing is voice phishing. These are phone calls with the intent of tricking you into giving away personal or financial information. For example, many people receive vishing calls from persons claiming to be from the Internal Revenue Service and give away their social security number or credit card number.
Angler phishing involves social media. Perhaps you’ve gotten a Facebook message from a friend that just says ‘Is that you?’ and a link to a video. That video link is most likely malicious!

Phishing is the most common cybercrime and most data breaches involve phishing.
According to recent research from Proofpoint, an email security leader, 75% of organizations around the world experienced a phishing attack in 2020.
If you are a phishing attack victim, the results can be disastrous. Your information is valuable. Company information is valuable. As phishing attacks become more sophisticated, you need to remain vigilant and carefully review emails for legitimacy.

1
Microsoft 365 and Google Workspace are great options!
2
Very important!
3
We like Proofpoint, but there are many options to choose from
4
– On-going security training
– Phishing simulation tests
5
Set up auto-update when possible
6
Password managers make this easy! We like 1Password or LastPass.
8
See below!
We can help!
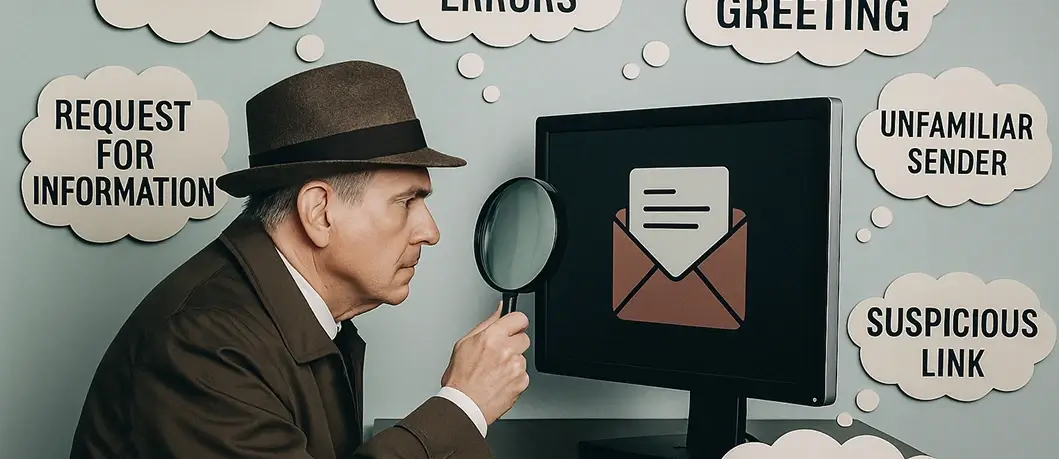
Even with the best email security programs, phishing emails are going to get through. Attackers are just that good! Every time you open an email, ask yourself:
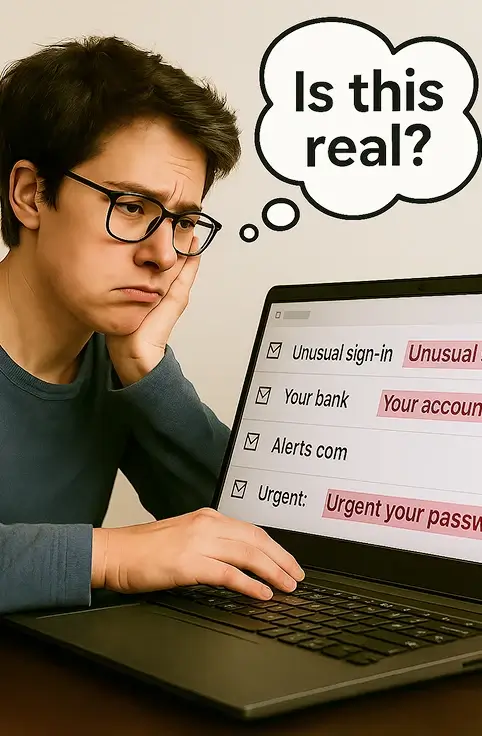
According to KnowBe4, these were the most common emails that users received and reported to their IT departments as suspicious:
So what should you do if you suspect phishing? Follow your company’s guidance if they have a policy. Here are some general recommendations:
No matter how good your email scanner is, highly targeted attacks can still get through. That’s why it’s super important to train your staff about phishing.
Here are two completely free websites that can both teach users how to spot a phishing attack AND test whether they would get fooled or not:
Company leaders, this section is for you.
You can install all of the top-notch technical solutions to combat phishing, but you’d be missing a critical piece of the puzzle. Your users. They are the last line of defense against phishing attacks. So what can you do to help them?

Here are a few ideas:
You do not want your employees to fall victim to a phishing attack. It’s important that your users feel comfortable bringing these sorts of situations to your attention. Empower them to make the right decisions!
There are many types of phishing attacks, but they can all devastate an individual or business. Be cautious before clicking any links, and never give personal or financial information unless you are 100% sure it is safe to do so.