As our work moves online and becomes more digital, our risks are changing. In recognition of this fact, registered investment advisors must take cybersecurity seriously. The SEC cybersecurity guidance lays out clear directions for taking cybersecurity risks seriously. And one of the biggest threats to your firm today is phishing.
The SEC Cybersecurity Guidance seems quiet on the topic of phishing. Take a closer look, though, and you’ll see that phishing is an important part of the guidance.
For example, the guidance says firms must have “policies related to penetration testing.” Phishing is a very common way hackers penetrate firms. Your phishing plan needs to be part of these penetration testing policies.
The SEC cybersecurity guidance also requires “periodic risk assessments to identify cybersecurity threats/vulnerabilities…” Again, phishing is a threat to your firm right now. Any good risk assessment will spot phishing as a high risk, high likelihood scenario.
So while the guidance isn’t specific, phishing is a very serious cybersecurity matter. The SEC has issued a number of other publications about phishing:
- A report of cyber-related frauds against public companies
- Recent announcements about SEC-themed phishing campaigns
- Investor publications like “’Phishing’ Fraud: How to Avoid Getting Fried by Phony Phishermen”
We recommend that all firms focus on six things to adequately combat phishing:
- Teach your staff what phishing is
- Train them how to spot a phishing message
- Teach your staff about the tricks that attackers use
- Make sure they know what to do if they suspect phishing
- Test your staff to make sure they understand all of the above
- Implement a number of firm-wide measures to combat phishing
Let’s walk through each of these in detail.
What Is Phishing?
Ever receive a phony or fraudulent email or a link to a suspicious looking URL? If so, you’ve already been the target of phishing.
Phishing is the #1 cause of data breaches. It’s also one of the most common tactics criminals use to steal data and money.
Attackers do anything and everything to evoke a false sense of trust. This allows them to leech valuable information from unsuspecting victims.
Oftentimes, phishers impersonate trusted, well-established companies by appropriating the use of logos, branding, employee names, and business names.
What is it about phishing that’s so appealing?
Simple: it works.
Individuals caught in phishing scams may unknowingly reveal highly sensitive information. This subjects their personal and professional lives to an incredible amount of risk.
Attackers can trick you into giving up:
- social security numbers,
- financial account numbers or accounts, or
- even login information to online financial systems.
But you can fight back. Here’s how.
Teach Your Staff Six Phishing Red Flags
Unfortunately, no technical solution is 100% accurate against stopping phishing.
That’s why the fight against phishing starts with your users.
To follow the SEC Cybersecurity Guidance, teach your staff how to spot a phishing message.
Each time you open an email, ask yourself:
(1) Does the email contain an attachment?
If yes, consider it high risk.
(2) Does the email contain a link?
If yes, consider it high risk.
(3) Is the email asking you to do something with money?
A couple of examples:
- An email seems to come from your CFO, asking you to pay an invoice or wire some money immediately.
- An email seems to come from your CEO, asking you to buy an iTunes gift card.
Here’s an example…
(4) Does the email have bad or unusual grammar?
For many attackers, English is not their first language, and it shows in their writing. Here’s an example:
(5) Does the email tug at your emotions?
For example, attackers often use one of these tricks:
- Urgency (“I need this wire right away or I’ll lose this real estate deal”)
- Confidentiality (“please don’t tell my partner about this” or “this is a confidential merger”)
- Hardship (“Help, I lost my wallet while traveling”).
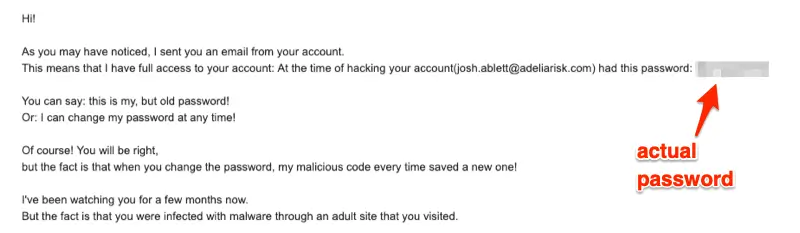
(6) Is the email trying to make you think you’ve been “hacked”?
There have been a lot of these recently. They seem very convincing because they may actually have one of your old passwords.
Here’s an example:
(7) Does the email just “feel” wrong?
If anything looks out of place, be cautious. Weird website addresses. Broken images. “Hey, why the heck am I getting Netflix emails at work?” Anything weird — trust your instincts.
Teach Your Staff Tricks Attackers Use
Phishing messages use all types of tricks to get you to lower your guard. Here are some of the more common examples.
(1) Spoofing an email address.
It is ridiculously easy to make an email appear like it comes from anyone you want. DON’T BE FOOLED just because an email SEEMS to come from a trusted vendor or someone inside your company.
PRO TIP: CEO fraud is a huge problem. An email will appear to come from your CEO asking you to pay an invoice or wire money away. ALWAYS pick up the phone and call your CEO directly to confirm any requests like this.
(2) Appearing to come from an authoritative company.
Hackers KNOW you’re more likely to open an email that appears to come from Google, Facebook, or Docusign. They will create emails that look REMARKABLY accurate. Don’t be fooled!
Here’s an example:
(3) “Sent from my iPhone.”
Attackers will add “Sent from my iPhone – please excuse mistakes” to their emails. This is an attempt to get you to lower your guard about bad grammar or poor spelling. Don’t be fooled!
What to Do If You Suspect Phishing
If your firm complies with the SEC cybersecurity guidance, you should have an incident response procedure.
Always follow your firm’s specific guidance over general guidance you find online.
Here are some general recommendations.
(1) Figure out who actually sent the email.
Look very carefully at the “from” address on risky emails. It’s easy to impersonate people that you trust.
The instructions for finding the *real* sender vary by system, so ask your IT team if you don’t know how to do this.
PRO TIP: Click the button to “Reply” to an email, but don’t actually send it. You should be able to see the email address that you’re responding to.
(2) Be aware of “typosquatting.”
Attackers will register domains that look tricky and are similar to legitimate domains. Here are some great examples:
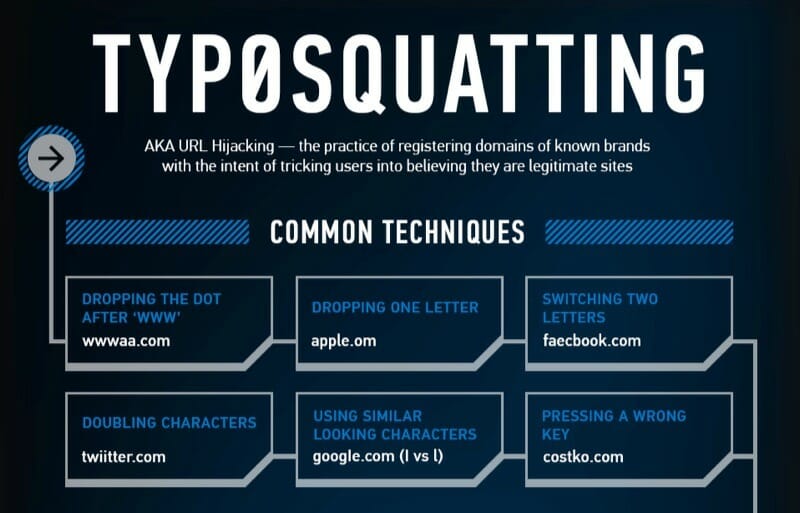
image courtesy of: https://www.anomali.com/resources/infographics/typosquatting-more-than-just-a-typo
(3) Hover over links before clicking.
If you hover your mouse cursor over a link in the email, you’ll see where it goes before you click on it. This is a great way to find tricky links before you click.
You can read more about this in our article about hovering over links.
(4) Check with someone technical.
If you’re in doubt, talk to your IT person or the person in your office who is most comfortable with technology. They’ll be able to figure out whether the email actually comes from a legit source or not.
PRO TIP: Checking emails is safer on mobile devices. iPhones and recent Android phones use something called sandboxing. Sandboxing makes it incredibly hard for malware to hack your phone. Some security experts only ever check their email on their iPad.
One caveat – this protects you from malware. It won’t help you at all if a phishing email tricks you into giving up your password.
(5) Scan attachments.
Not sure about whether an attachment on an email is legit? Here’s a trick that’s a bit technical, but will help you be safer.
You can upload attachments to VirusTotal, and they’ll scan the file against 59 different virus scanning engines. It’s not 100% foolproof, but it’s a good start. Give it a try at virustotal.com.
Check Yourself Before You Wreck Yourself
Here’s the thing about phishing. You have no way to know how good you’re doing until it’s too late. For clients of our SEC Cybersecurity Service, we run phishing tests for you. We’ll send fake phishing messages to your team, and see who clicks. Then, we can take appropriate steps based on who clicks.
There are also a number of pretty good phishing quizzes online. A quick search should help you find some. We also really like this new test from Google.
What Should Firms Do About Phishing?
You’re not done yet. The list of recommendations above is what you should teach each member of your staff.
Here are the best practices we recommend to investment firms to comply with SEC Cybersecurity Guidance:
- Get a secure email gateway
- Use an email hosting service that offers built in protection (like Office365 or G Suite). This is a great second-layer defense combined with secure email gateways.
- Email servers need to be set up properly! For our clients, we review all of the email server settings and make sure they’re configured properly.
- Hire a firm (like ours) to do fake phishing tests to see which people are likely to click on phishing emails. Hold targeted training for those who fail repeatedly.
- For our clients, we provide on-going training to staff on how to spot phishing messages.
- Keep your computers patched. Most firms have a lot of vulnerabilities on their computers, and don’t even realize it.
- Set up your email system so it gives you warnings that an email comes from an external source.
PRO TIP: If you see that warning on an email from the CEO, you know it’s probably a fake!
Conclusion on SEC Cybersecurity Guidance
Remember: YOU are the last line of defense against a horrible phishing attack. Please use this information to be safer and comply with the SEC Cybersecurity Guidance.
Don’t have time to implement all of this yourself? We can help. Our SEC Cybersecurity Service is the easiest way to build a strong cybersecurity program.
For additional information on protecting your business from phishing and other data scams, book a time to speak with us here or give us a call at 888-646-1616.

