Smishing, also called SMS phishing or text message phishing, is a growing problem for many individuals and businesses. Smishing is a phishing message that uses your cell phone as the attack platform. Cyberattackers use smishing to do the following:
- Get you to click a malicious link
- Gather personal information
- Get you to do something like send them money or buy gift cards
Like phishing emails, smishing messages are not always obvious, and can sometimes be harder to detect. We often identify phishing emails by looking closely at the sender’s name and email address, or by inspecting the link before clicking. It’s impossible or extremely hard to do those things with a text message.
What is Smishing?
Smishing is short for SMS phishing. SMS is Short Messaging Service, which is a popular text-based messaging service. Almost all cell phones support SMS.
Typically we think of email when it comes to phishing – but smishing continues to gain popularity. One big reason: SMS open rates are as high as 98% as reported by Gartner. This is also why you’re seeing more text messages from businesses promoting sales or reminding you of appointments.
Why else is smishing a popular phishing vector? It’s easy to find phone numbers – or just make them up! Email addresses are not usually limited by size, and can contain letters, numbers, and symbols – phone numbers are limited to numbers and can only be 10 digits. It’s easy to string together random digits to send a smishing message.
At the end of this article, we have tips to defend against smishing. But there are two important tips we will share now: DO NOT click links in SMS messages, and DO NOT respond to texts from people they don’t recognize.
Let’s check out some examples of smishing!
Examples of Smishing
The examples and screenshots below are not at all an exhaustive list. There are unfortunately so many types of scams that it’s impossible to keep an updated list. But these are the more common examples that you should look out for.
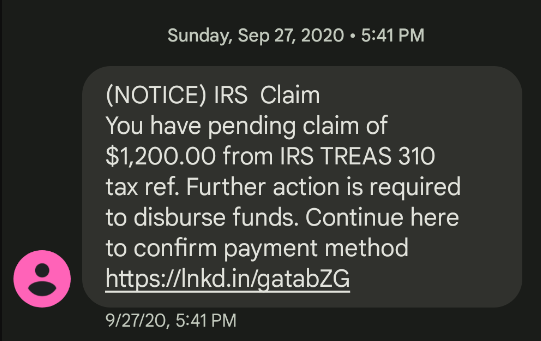
IRS
IRS scams are usually pretty popular January-April of each year. The example below came during the COVID pandemic relief checks disbursement and was promising $1200.
Other IRS scams include the threat of an audit, unclaimed refund money, that you’re being charged back taxes, or that there is an issue with your refund.
Clues: Seeing the letters ‘IRS’ usually makes people wake up and pay attention, and the promise of $1200 could make anyone click the link. If you get any sort of message about or from the IRS, it’s best to visit the IRS’s official website to learn more. Do not click the links in the messages, even if you’re pretty sure it will go to a legitimate IRS website.
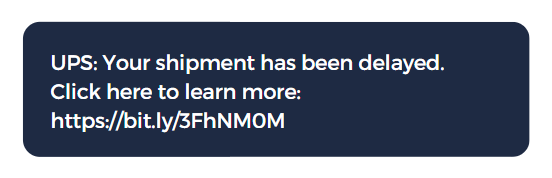
FedEx, UPS, USPS
Hackers know that you care about your purchases or gifts being delivered on time. So getting a shipment delay message could compel you to click a link to learn more.
Clues: If a message seems urgent, take pause. They are betting on you wanting to know more right away and clicking the link. But would UPS use a link shortening service like Bitly? Probably not. It’s best to log into UPS’s site directly to check for shipment status.
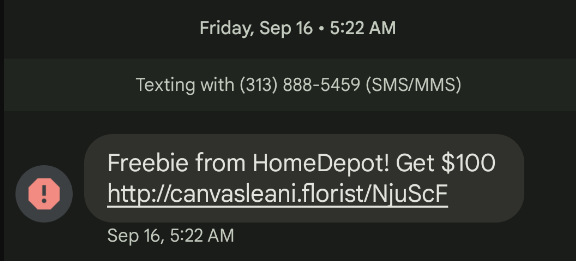
Amazon or other big name brands
Text messages from big brands like Amazon, Home Depot, Walmart, hotels or airlines are most likely smishing. These are not legitimate.
Clues: The possibility of FREE things can be a clue that this is smishing or spam. Also, Home Depot has a space between the words, the URL is not https, and doesn’t resemble Home Depot’s URL at all.
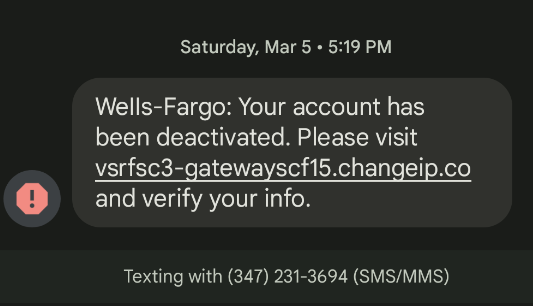
Banks
If your banking account had actually been deactivated, you would not simply receive a text message. If you are concerned this message is true, call your bank directly.
Clues: Wells Fargo doesn’t have a hyphen, and the link is a gobbled up mess.
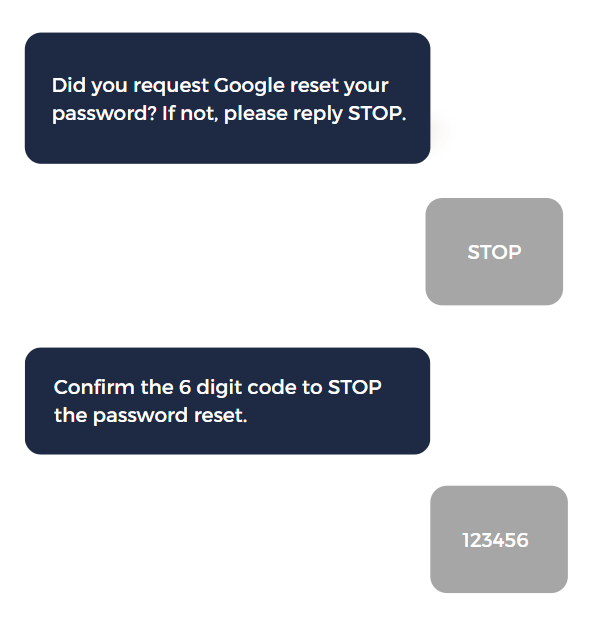
Password Reset
The example below is unfortunately a very common situation. Here the example is from Google, but this scam works with just about any company: PayPal, airlines, hotels, banks, investment companies, retail stores, social media sites.
You may think this is a harder scam to pull off, since it requires a hacker to have both your email address and phone number. But guess what – it’s not that hard to find both.
Basically it works like this: a hacker sends you the first message regarding a password reset. They provide simple instructions: just reply STOP! Meanwhile, they are trying to log into your account with your email address and trigger the ‘forgot password’. This sends a SMS message to your phone. If you send them that 6 digit code, they have access to your account.
This is the perfect example of how multi-factor authentication (MFA) is not bulletproof. You just gave the MFA code away. You should never give MFA codes to anyone.
Clues: Any message about a password reset deserves pause, and a text message asking for a verification code is definitely suspicious.
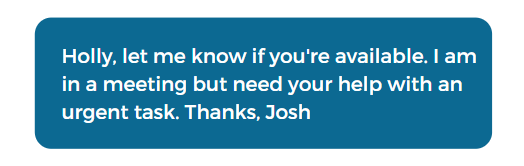
Work Contact
One of the common smishing attacks for businesses involves a message from the “CEO” asking an employee to take care of an urgent task. How is this happening?
The prevailing theory is that scammers are trolling LinkedIn to watch who works at which company, and then use publicly available telephone number lookup services to find the number to text.
Anyone can look up a company on LinkedIn or Google and find the name of the CEO or other leader, as well as the names of other employees.
Most employees would be happy to make a good impression on the CEO and would gladly try to help them out. That’s why this smishing scam works.
Sometimes these scams end with the “CEO” asking the employee to wire money to a certain account, purchase gift cards and provide the numbers, give away private company information, and a million other things. Hackers are betting on you being a kind person trying to help the CEO or company leader.
Later in this article we have tips on preventing smishing attacks, and many of them pertain to this specific situation.
Clues: A random text from the CEO is suspicious, and the “urgent task” reeks of phishing.
This example is not just limited to work! Thanks to Facebook, it can be easy to see who is related to who. A hacker could easily contact a grandmother pretending to be a relative in need of money. The FTC has a great article about this: https://consumer.ftc.gov/articles/scammers-use-fake-emergencies-steal-your-money
Facebook Messenger
Although we’re talking about smishing and SMS messages specifically, the same types of messages are leaking into other messaging methods, like Facebook Messenger. The same advice for avoiding smishing applies to Facebook Messenger. Even if it looks like a message from a friend, do not click links or provide personal information.
Other smishing examples
There are many other popular smishing topics and scams out there, including: messages related to the COVID pandemic or vaccines, US or State Elections, Student Loan Forgiveness, or any other hot topic at the moment.
How to prevent Smishing
So what can you do about smishing?
Here are some tips to consider:
- Don’t put cell phone numbers on your company website
- Don’t put cell phone numbers in your email signature
- Share examples of smishing with your team
- Train your team on how to report scam phishing messages
- Train your team to NEVER respond to a text from someone they don’t recognize, or someone who works for the company who they’ve never texted with before.
- Train your team on safe communication channels – maybe that’s Slack, Teams, Google Chat. If an employee receives a text from a coworker, they can confirm legitimacy via the safe communication channel
- Train your team to never click on links sent via text message, ever.
- There are services that can supposedly scrub personal details (like phone numbers) from the internet. The problem is that our information is shared in so many places that it’s unlikely a service would get them all.
Unfortunately, these tips won’t entirely stop it, but it will minimize the chances of one of your employees falling for a smishing text.
Conclusion
Smishing is proving to be an effective cyberattack. Protect yourself and your company by learning about common smishing attacks, teaching your staff to identify and avoid these scams, and by creating a strong cybersecurity awareness culture.
Adelia Risk’s Virtual CISO Service can strengthen your company’s cybersecurity program through assessments, audits, monitoring, and training. We specialize in working with small and midsize businesses: https://adeliarisk.com/virtual-ciso-service/