Phishing scams can cripple an organization – so it’s important to know how to recognize, prevent, respond, and report phishing. You may think phishing scams are obvious, but this is simply not the case. Phishing scams can be incredibly convincing.
This article will dive into some typical phishing red flags, our best phishing prevention tips, what to do if you’re a victim of phishing (whether with your personal accounts or work accounts), and finally how to report phishing to the proper agencies.
How to recognize phishing
Phishing is a cybercrime where you are tricked into giving personal information or clicking a link. Sometimes they are obvious, but sometimes they are expertly crafted and can trick just about anyone.
There are many types of phishing scams, including smishing, spear phishing, vishing, and more.
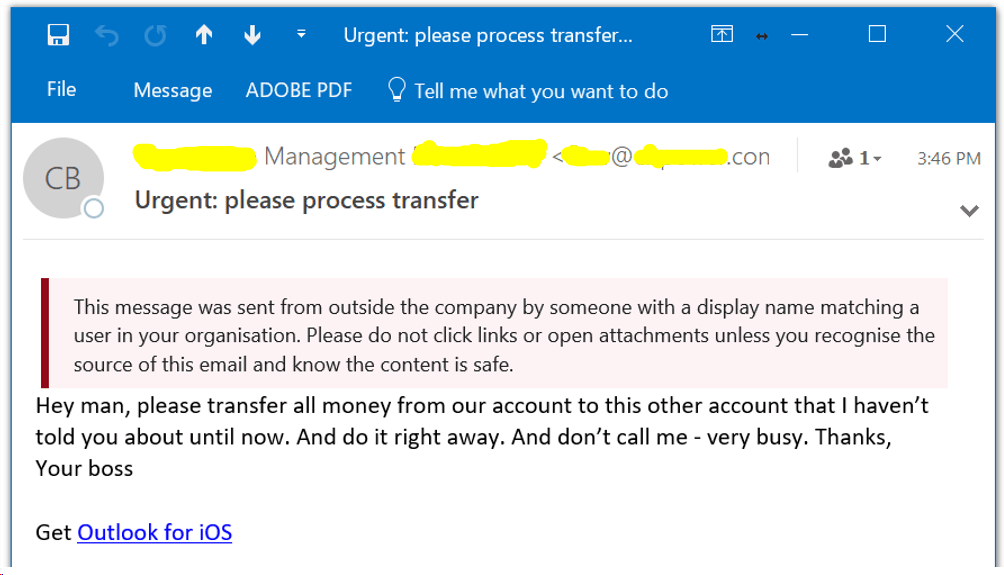
Be on the lookout for these typical phishing ‘red flags’:
- Emails with attachments
- Messages with links
- Messages asking you to do something with money (wire transfer, buying gift cards, etc.)
- Bad or unusual grammar
- Messages that tug at your emotions (sense of urgency, payment was denied, pandemic-related)
- Messages that make you think you’ve been hacked (password reset, messages about your computer being infected)
- Messages that just ‘feel’ wrong
If you aren’t 100% sure the sender is who they say they are, don’t reply or click any links.
Phishing prevention tips
There are many tips related to phishing prevention. It seems obvious, but the best prevention tip is being cautious before clicking any links or giving out any personal information. But what else can you do?
- Use email services with anti-spam features, like Microsoft 365 or Google Workspace
- Use multi-factor authentication wherever possible
- Keep computers and software up-to-date
- Use the hover link method before clicking links
- Provide training for employees: security training and phishing simulation tests
What to do if you’re a victim of phishing
If you think a scammer has your sensitive information, like a credit card number, social security number, or login/passwords, visit https://www.identitytheft.gov/#/Info-Lost-or-Stolen to see the specific steps you should take.
If you think a scammer has access to your work computer or mobile device, contact your IT department ASAP. They should have steps to follow in these types of situations.
If you think a scammer has access to your home computer or mobile device, the first thing you should do is disconnect from the Internet (enable airplane mode or disconnect from Wi-Fi). Then, take your computer to a trusted IT firm to have it properly scanned and cleaned. Ask friends and family for recommendations.
How to report phishing
Ok, you know your company has been a victim of a phishing scam. What do you do next? There are a number of places to report the scam.
Forward the phishing message to these places:
Report the incident:
Google: https://safebrowsing.google.com/safebrowsing/report_phish/?hl=en
Microsoft: https://www.microsoft.com/en-us/wdsi/support/report-unsafe-site-guest
Norton: https://submit.norton.com/?type=URL
Federal Trade Commission (FTC): https://reportfraud.ftc.gov/#/assistant
FBI / Internet Crime Complaint Center: https://www.ic3.gov/Home/FileComplaint
Did the incident involve the use of a lookalike domain? Be sure to look up where the domain was registered and look for the Abuse Reporting Procedures, so you know how to get the lookalike website/domain removed. For example, here is GoDaddy’s Reporting Abuse page: https://www.godaddy.com/help/reporting-abuse-27154
Why you should report phishing
It’s true, there are many places to report the phishing incident to. Why bother? Well, there are a few reasons:
- Reporting the incident can help prevent this from happening to someone else
- By reporting the incident quickly, there is a greater chance of reducing future harm to your clients, contacts, and coworkers
Think of it this way: if a hacker was emailing all of your contacts to update their billing on a webpage, wouldn’t you want that webpage taken down immediately? That’s why you want to start the reporting process as soon as possible.
Cyber attackers move quickly, which is why you need to move as quickly as possible to contain the incident.
Adelia Risk vs. Phishing
Phishing attacks are common and sadly, successful. The phishing prevention tips listed above? We incorporate all of those into our Virtual CISO service: monthly phishing simulation exercises, security training, vulnerability scanning to look for out-of-date software, and more.
We work almost exclusively with companies in high-regulated industries like financial services, healthcare, and manufacturing. Learn more about our 60-point cybersecurity framework and what our clients have to say about working with us.



