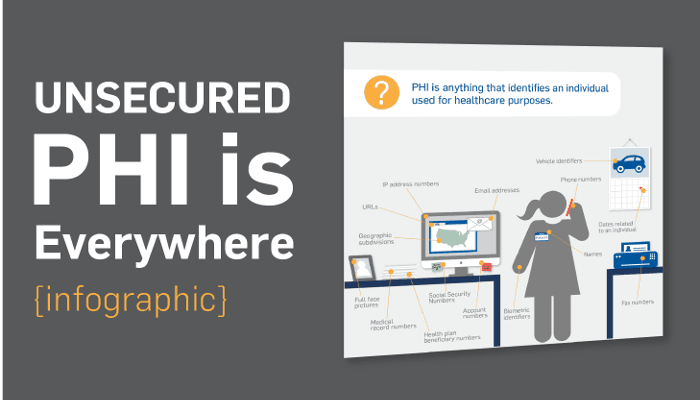
The first step in performing a HIPAA security risk assessment is to be sure you understand what Protected Health Information (PHI) your practice has.
Here’s how Wikipedia defines PHI: “Under the US Health Insurance Portability and Accountability Act (HIPAA), PHI that is linked based on the following list of 18 identifiers must be treated with special care:
- Names
- All geographical identifiers smaller than a state, except for the initial three digits of a zip code if, according to the current publicly available data from the Bureau of the Census: the geographic unit formed by combining all zip codes with the same three initial digits contains more than 20,000 people; and the initial three digits of a zip code for all such geographic units containing 20,000 or fewer people is changed to 000
- Dates (other than year) directly related to an individual
- Phone numbers
- Fax numbers
- Email addresses
- Social Security numbers
- Medical record numbers
- Health insurance beneficiary numbers
- Account numbers
- Certificate/license numbers
- Vehicle identifiers and serial numbers, including license plate numbers;
- Device identifiers and serial numbers;
- Web Uniform Resource Locators (URLs)
- Internet Protocol (IP) address numbers
- Biometric identifiers, including finger, retinal and voice prints
- Full-face photographic images and any comparable images
- Any other unique identifying number, characteristic, or code except the unique code assigned
by the investigator to code the data
Is Your Business HIPAA Compliant and Secure? Don’t Wait for a Breach, Start your cloud security journey with our comprehensive audit.. Our specialists are committed to helping your business stay safe and seamlessly achieve HIPAA compliance and encryption requirements.

Where is your PHI?
Next, build a list of all of the places you store PHI. Here are common places we’ve seen at other clients:
- Desktop computers
- Laptop computers
- Servers in your office
- Servers at a vendor or off-site location
- Emails you send internally
- Emails you send externally
- File-sharing sites like Dropbox or Google Drive
- Business applications like Salesforce.com, electronic medical records, etc.
- Mobile devices like iPhones, Androids, or tablets
- Fax machines / Photocopiers / Scanners
- Old school tech like pagers, dictation machines, etc.
- File room(s) or Filing cabinets in hallways or people’s offices
- Paper files stored off-site
- Backup files on-site or off-site
- USB / thumb drives
- Medical devices (like x-ray machines, EKG, EEG, etc.)
- In a website you run or someone runs on your behalf
- In a database you run or someone runs on your behalf
- Transcriptionist service
- Billing service
- Collections service
- Hosted EMR / EHR provider
- E-Prescriptions
- Electronic Vaccine Records Exchanges
- Hosted Email Service
- Hosted Fax Service
- Hosted Online Document Storage Service
- IT company/person
What should you do next?
Get some free help! Check out our free 42-Point Checklist for ways to make your practice HIPAA compliant.
Talk to us!
Have questions or feedback? Please share them in the comments below.
Like this article? Share it!