Has your company completed a cybersecurity risk assessment? If you haven’t, you should definitely consider doing it soon. A cybersecurity risk assessment is a great way to learn how to safeguard your company and data from cyberthreats and data breaches. This article will explore what’s involved with a cybersecurity risk assessment, as well as our favorite templates, tips, and articles to start the process on your own.
What is a cybersecurity risk assessment?
A cybersecurity risk assessment can help your company determine its ability to protect its data from cyberattacks. There are many methodologies to choose from. But overall, a cybersecurity risk assessment is the best way to identify risks and prioritize ways to reduce those risks.
If you work in a highly-regulated industry, oftentimes the risk assessment will incorporate best practices based on specific cybersecurity regulations. For example, US government contractors have CMMC requirements, investment advisors have SEC recommendations, and healthcare entities have HIPAA standards.
Why should you perform a cybersecurity risk assessment?
If you care about your business, you’ll perform a cybersecurity risk assessment. Assuming your company isn’t a target is, frankly, naive. If your company has a website and/or uses email or any other cloud service, you need to take cybersecurity risk seriously.
Who should perform the cybersecurity risk assessment?
This will depend on the size of your organization. Typically, large companies have dedicated in-house risk teams. But smaller and midsize companies may not have the resources or the need to have in-house risk teams. Instead, they’ll need to outsource this task.
Something you should know: any cybersecurity firm or Virtual CISO service will have their own method for calculating cybersecurity risk. There isn’t a standard that we all follow. But generally, all risk assessments have a similar goal: identify the risks and have a clear plan to mitigate those risks. If a company is offering a risk assessment that simply provides a score, run away. You need to make sure the company will offer clear recommendations on how to address the gaps in the assessment. Also, if your industry has specific cybersecurity regulations, make sure the risk assessment takes those standards into account.
Small and midsize businesses are at risk
It’s far too easy to assume you don’t need to look at your cybersecurity risk. We hear from companies all the time that have employees who think IT and cybersecurity controls are overkill and only cause paranoia. This is not the case.
We’ve seen even small one-person companies fall victim to cyberattacks that literally cripple their business. According to Forbes, small businesses are three times more likely to be targeted by cybercriminals than larger companies.
The Basics of a Cybersecurity Risk Assessment
There are basic steps to any cybersecurity risk assessment: establish scope, identify risks, analyze and prioritize risks, documentation.
Below are some of the best articles about cybersecurity risk assessments, what information you should consider, and how to get started (hint: it’s an assessment before the actual assessment!)
5 Cybersecurity Risk Assessment Templates and Tips
Because we’re a cybersecurity company, we’re a bit biased and think you should have a third party evaluate your company’s cybersecurity risk. But, if you want to learn more about the different processes and templates, or if you want to start the process yourself, below are a few templates to get you started.
Best Pre-assessment Questions
Upguard’s How to Perform a Cybersecurity Risk Assessment
Upguard has an excellent article with thorough details about each step of the risk assessment. They start with some excellent pre-assessment questions to consider, like:
- What data do we collect?
- How and where are storing this data?
- How do we protect and document this data?
- And so on
This is a great first step because it allows you to think through what critical information you are using and storing at your company. This is how we start our Virtual CISO engagements as well, because knowing WHAT to protect helps you create an effective cybersecurity strategy.
https://www.upguard.com/blog/cyber-security-risk-assessment
More Pre-assessment Questions
Cyphere’s Cybersecurity Risk Assessment
Yes! Another article with good pre-assessment questions. Doing a thorough pre-assessment will help you complete a thorough risk assessment. You need to understand what you’re protecting and why you’re protecting it.
Cyphere recommends considering the following:
- Would your organization incur any legal or financial penalties in case of data loss, theft or exposure?
- What would be the implications of a cyber attack, data breach or theft? Would it be reputational, financial, legal or all of them?
- What is the impact of data loss or exposure on the organization’s revenue?
- What costs are associated with recovering the information, whether from backups or recreating the information?
https://thecyphere.com/blog/cyber-security-risk-assessment/
Thorough Checklist to Get Started
Netwrix’s Information Security Risk Assessment Checklist
In exchange for your email address and phone number, Netwrix will give you access to its Risk Assessment checklist.
This is a pretty thorough checklist! It gives you the steps needed to complete a risk assessment. Plus, it gives you examples to help you think through the steps. For example, instead of thinking of all the potential consequences on your own, use their list to get started:
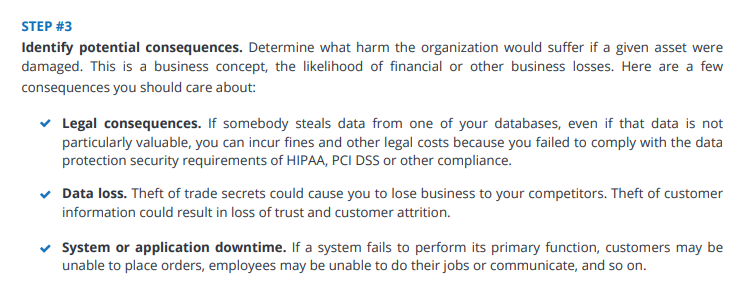
They also provide a simple way of documenting the results:
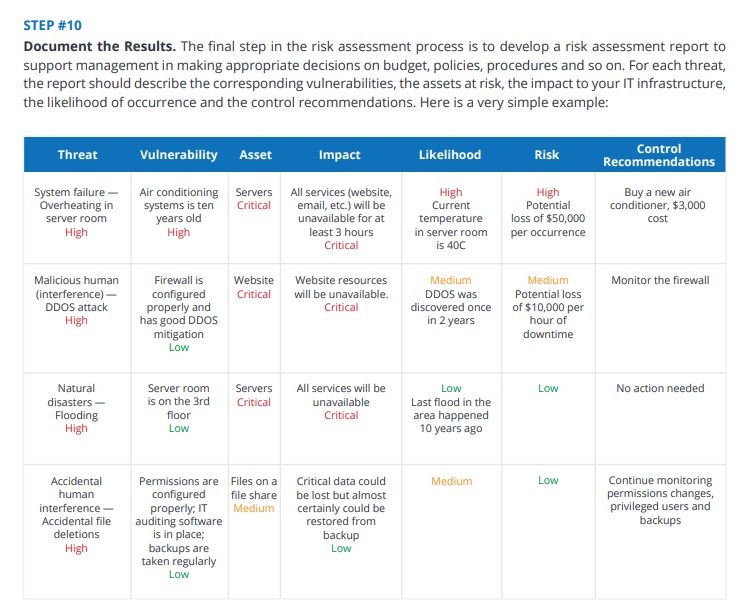
This one was definitely worth downloading!
https://netwrix.com/en/resources/guides/cybersecurity-risk-assessment-checklist/
What are the threats to consider?
Threats can usually be divided into smaller categories: man-made and natural.
Natural threats include: fire, flood, earthquake, rodent or insect infestation, and severe weather.
Man-made threats include: theft, unauthorized facility access, malicious code, phishing attacks, and more.
Unfortunately, there are so many threats to consider, and this landscape is constantly changing as cyberattacks evolve.
You may want to review your company’s Incident Response Policy in order to understand some of the incidents and threats that could impact your firm. Here’s an example:
- Violation of the company’s cybersecurity policy
- Unauthorized computer access
- DDoS event
- Misuse of service, systems, or information
- Malicious virus on the company computer
- Unauthorized network activity
- Lost or stolen computer or mobile device
There is also a large list of threats here: https://www.51sec.org/forum/tra-threat-risk-assessment/threats-list/
Documentation Ideas and Risk Treatment Plan
TechTarget’s How to Perform a Cybersecurity Risk Assessment
TechTarget does a nice job of summarizing the steps of a risk assessment, specifically when it comes to what information should be included when documenting the risks. They recommend including:
- Risk scenario
- Identification date
- Existing security controls
- Current risk level
- Treatment plan
- Progress status
- Residual risk
- Risk owner
For the Risk Treatment Plan, TechTarget outlines the three ways of doing this: 1) discontinuing the activity if the risk outweighs the benefits, 2) sharing the risk through cyber insurance or outsourcing those specific operations, or 3) using security controls or other measures to reduce likelihood/impact. Notice that ‘ignore the risk and hope it doesn’t happen’ isn’t one of the options!
The Necessary Risk Matrix
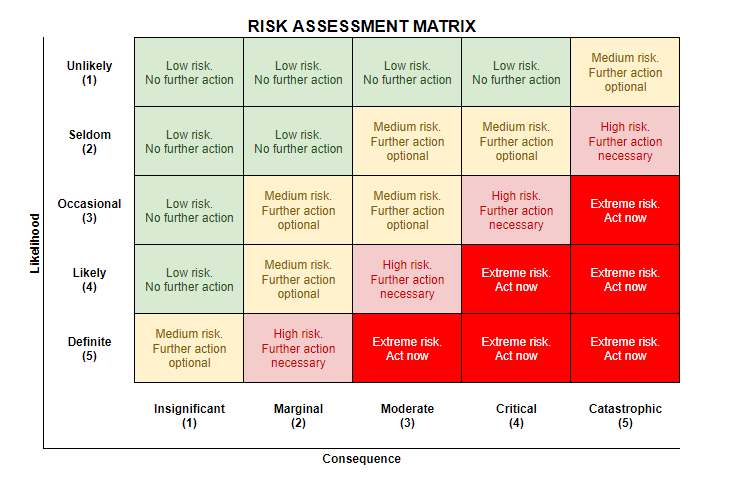
When analyzing risks, it’s important to prioritize them. How? With a risk matrix.
A risk matrix helps you understand risk level based on likelihood and consequence – if a certain risk is very likely and the consequence would be catastrophic, then this risk has the highest priority.
A risk matrix allows you to make decisions on what to fix first.
Why choose Adelia Risk for your cybersecurity risk assessment needs?
Adelia Risk’s Virtual CISO service is the best way for companies with 10-250 employees to drastically improve their cybersecurity. The initial gap assessment and annual risk assessments give stakeholders the right information, recommendations, and expert advice. We specialize in helping companies in highly-regulated industries like financial services, government manufacturing, and healthcare.



