Do you need help with CMMC compliance?
Guess what - so do tons of other US Government contractors.
In fact, over the next few years, 300,000 businesses will be required to dramatically improve their IT and cybersecurity due to CMMC.
We’re receiving requests every day from companies who need help with CMMC compliance. And we typically share information about the phases of CMMC certification, which we’ll outline below. It helps to look at what a CMMC project looks like and to understand what you’re signing up for.
The US Department of Defense (DoD) will require all vendors to have a cybersecurity maturity audit. Based on this audit, they will be assigned a rating from CMMC Level 1 to Level 5.
Starting in 2021, DoD Requests for Proposals (RFPs) will state “you must be CMMC level X.” This is a game changer. If your company isn’t compliant by award time, you will lose the business.
In 2017, US Government contractors were supposed to comply with NIST 800-171, which contained 100+ specific things to prevent cyberattacks and protect confidential government data.
Unfortunately, too many vendors used the ‘self assessment’ method and didn’t actually follow NIST 800-171. So the CMMC was created to add enforcement. There will be no self assessment option for CMMC compliance. You will be audited by a third party and assigned a CMMC level.
No, but they’re similar. In November 2020, the DoD came out with the Interim Rule. This requires companies to perform a NIST 800-171 self assessment, fill out some documentation, and upload a score into the DoD’s SPRS system.
This will all depend on your specific organization. See below for more information on the 5 maturity levels.
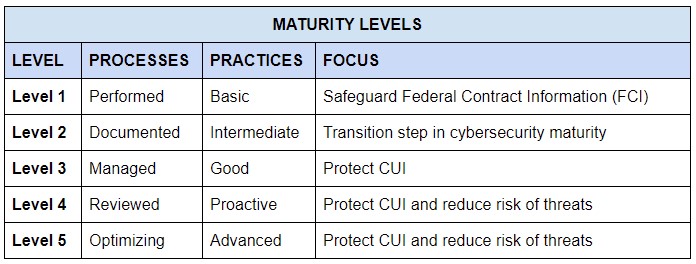
If you handle CUI, you will be required to get assessed at Level 3.
Here are the typical phases of a NIST 800-171 / CMMC project:
We help clients follow a structured process to find “Controlled Unclassified Information” (or CUI), which is the focus of CMMC. You can find the ever-changing list of CUI here: https://www.archives.gov/cui/registry/category-list
This needs to be done twice -- once for the 110 NIST 800-171 requirements and once for the 130 CMMC requirements to identify where the company is or is not compliant. You’ll need to review your current policies and procedures against NIST/CMMC controls.
A DoD-required project plan that outlines your action plan to fix your gaps. The POAM will outline all of the action items and timeline to achieve NIST or CMMC compliance.
A detailed security policy that identifies all of the ways you’ll keep CUI safe and what’s expected from employees. This needs to be done once for NIST 800-171, and then updated for CMMC. The SSP will list hardware, software, security measures, auditing processes, incident response protocols and more.
This includes one-time and on-going training for employees. We set up our clients with one-time cybersecurity training, monthly cybersecurity training videos and quarterly phishing simulation exercises.
This is by far the longest part of the project. You’ll need to implement all of the IT and cybersecurity fixes required to address all identified gaps. You made the POAM, and now you need to follow through.
CMMC compliance requires detailed evidence to prove that your SSP is fully implemented. This should be in place for 6 months before an audit.
In our experience, the key to success is executive client engagement. They're going to need to make a LOT of changes to pass an audit, and executive buy-in makes a world of difference.
Are you looking for help with CMMC Maturity Level 3?
Do you want to work with a firm where you get personal, expert attention?
Are you trying to figure out how to spend enough to be compliant without overspending?
If this sounds like you, we can help.
We've helped clients with cybersecurity since 2010 and with NIST 800-171/CMMC since 2017.
We offer a tried-and-true, repeatable process to find your gaps, build a plan, and work with you to get where you need to go.
Our CISO, Josh Ablett, is a CMMC-AB Registered Practitioner. Learn about our Virtual CISO services.